
Jessica Wright
Cybersecurity Threat Researcher
Professional Background
I Research the Threats Before They Reach You
My name is Jessica Wright. I am a cybersecurity threat researcher based in Washington, D.C., with a background in threat intelligence, IP reputation systems, and digital privacy law. Washington is not an accidental choice of location — being close to where data protection legislation gets written and lobbied has shaped how I think about cybersecurity. Policy and technical reality are rarely the same thing, and understanding both sides is what makes my research at Trust My IP different.
Before joining Trust My IP, I worked in threat intelligence — tracking how IP-based attacks are coordinated, how blacklists are built and maintained, and how threat actors rotate infrastructure to stay ahead of blocklists. That operational background means I do not just explain what a threat is. I explain how it actually moves, why it targets what it targets, and what the realistic options are to defend against it.
What I Focus On at Trust My IP
My research sits at the intersection of IP reputation, threat detection, and data privacy compliance. In practice, that covers a wide surface area. Here is where most of my work is concentrated:
- IP Blacklisting & Reputation Recovery: Understanding the mechanics behind how IPs get flagged — spam behavior, bot traffic, abuse reports, shared hosting contamination — and building practical, step-by-step delisting processes that actually work with real blocklist operators.
- Threat Intelligence & Attack Pattern Analysis: Monitoring how IP-based threats evolve — credential stuffing, scraping abuse, DDoS infrastructure rotation — and translating that into defensive guidance for businesses and individuals who are targeted.
- Data Privacy Law in Practice: Translating GDPR, CCPA, and emerging state-level privacy frameworks into what they actually mean for how your IP data is collected, stored, shared, and legally actionable — not what the law says in theory, but what it means for you on a Tuesday.
- IP Fraud Detection: Covering how fraud scoring systems work, what signals they use, and why a clean IP can still get flagged — and what to do about it when it happens to your business.
- Browser & Network Fingerprinting: Documenting the tracking methods that go well beyond IP addresses — canvas fingerprinting, font enumeration, WebRTC exposure — and how to audit your own exposure.
How I Approach Writing About Security
Cybersecurity writing has two failure modes. The first is being so technical that only specialists can use it. The second is being so simplified that the advice does not actually hold up in a real situation. I try to hold the line between those two extremes — giving you enough of the underlying mechanics to understand why something works, without turning every guide into a research paper.
I also try to be honest about uncertainty. Security is not a solved problem. Threat landscapes shift. A blocklist delisting process that worked reliably six months ago may have changed. When that happens, I update my guides and I say what changed. If a tool I previously recommended has been acquired, changed its privacy policy, or had a documented incident, I note it. The goal is to be accurate, not to be consistent with what I said before.
Why Washington D.C. Shapes My Perspective
Living and working in D.C. puts you close to the legislative process in a way that changes how you read privacy law. I have sat in on public hearings, followed rulemaking processes through the FTC and state attorneys general, and watched how the same data protection language gets interpreted completely differently in enforcement versus in compliance writing. That context shows up in everything I write about GDPR, CCPA, and the broader question of what rights you actually have over your own data — versus what rights exist only on paper.
Outside the Research
When I am not tracking threat actor infrastructure or reading through the fine print of a new privacy regulation, I spend time in my garden — which is, genuinely, the most low-stakes environment I encounter in a given week. I also spend more time than I should in D.C.'s older libraries and archives. There is something useful about studying how information has been controlled, protected, and weaponized throughout history. The mechanisms change. The motivations rarely do.
Expertise Focus
"Jessica Wright is a cybersecurity threat researcher based in Washington, D.C., specializing in IP reputation systems, blacklist recovery, threat intelligence, and digital privacy law. Before joining TrustMyIP, she worked in threat intelligence tracking IP-based attack infrastructure and blocklist dynamics. Her guides combine operational security research with practical privacy compliance guidance drawn from direct experience with GDPR, CCPA, and U.S. federal data protection frameworks."
Article Impact
Latest from Jessica

Check If Your IP Is Residential or Datacenter: The Complete 2026 Guide

How to Check if Your VPN IP is Blacklisted: Complete 2026 Diagnostic Guide

How to Warm Up an IP Address for Email Marketing: Complete 2026 Guide

Best IP Reputation Monitoring Tools 2026: Free and Paid Options Compared

IP Reputation vs Domain Reputation: The Difference That Determines Your Inbox in 2026

How Long Does an IP Blacklist Last? Every Major List Explained (2026)

What is an Email Blacklist and How to Avoid It: Complete 2026 Guide

How to Check if Your IP is Failing SPF, DKIM & DMARC: Complete 2026 Guide

How to Delist Your IP from Spamhaus Blacklist: Complete 2026 Fix Guide
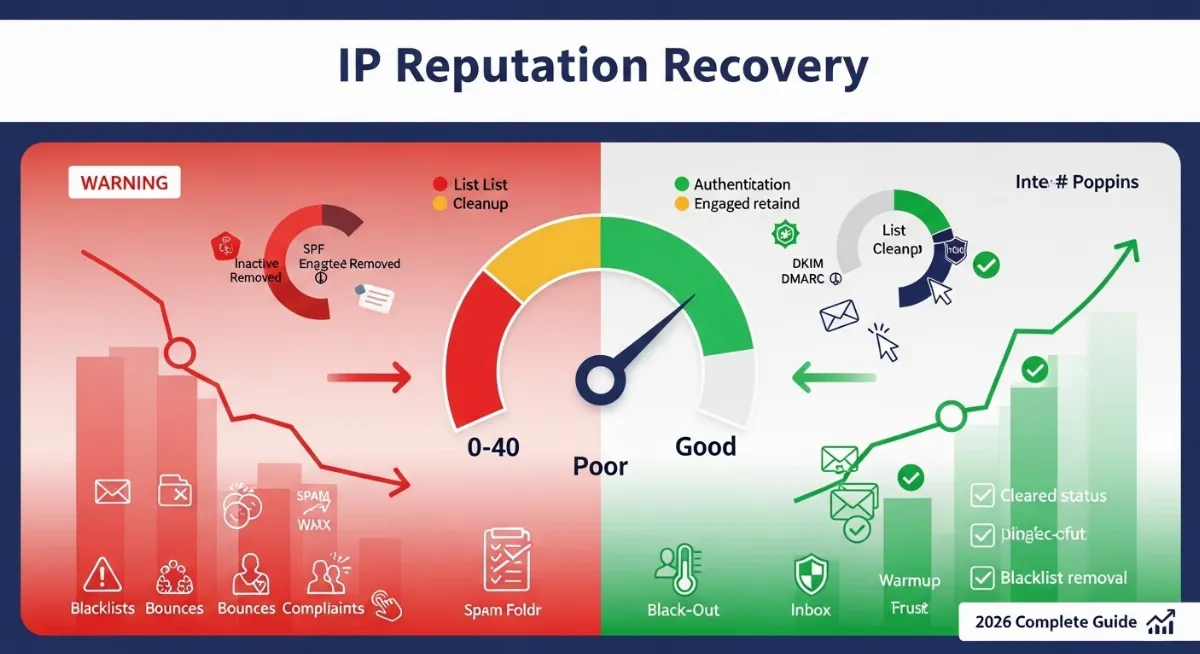
How to Improve Bad IP Reputation Score: Complete Recovery Guide 2026

550 An RBL Has Blocked the Sender's IP Address: Complete Fix Guide (2026)

What is IP Spoofing and How to Detect it?

How to Protect Your IP Address from Hackers: 7 Proven Methods (2026)
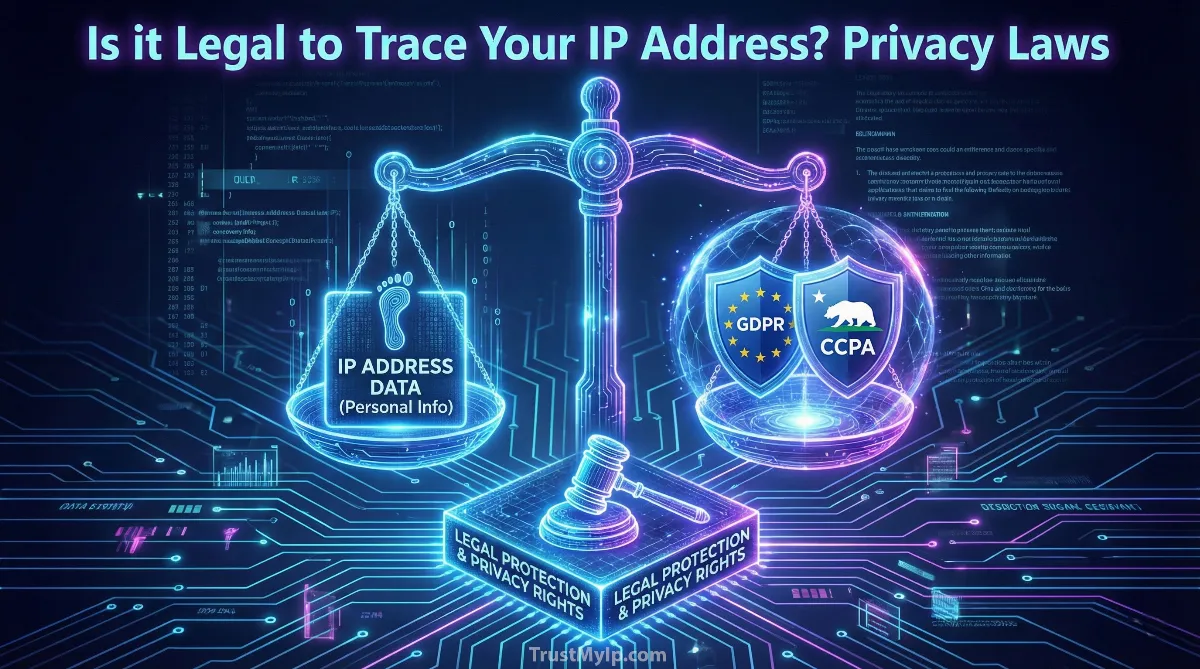
Is it Legal for Someone to Trace Your IP Address? [2026 Privacy Law Guide]
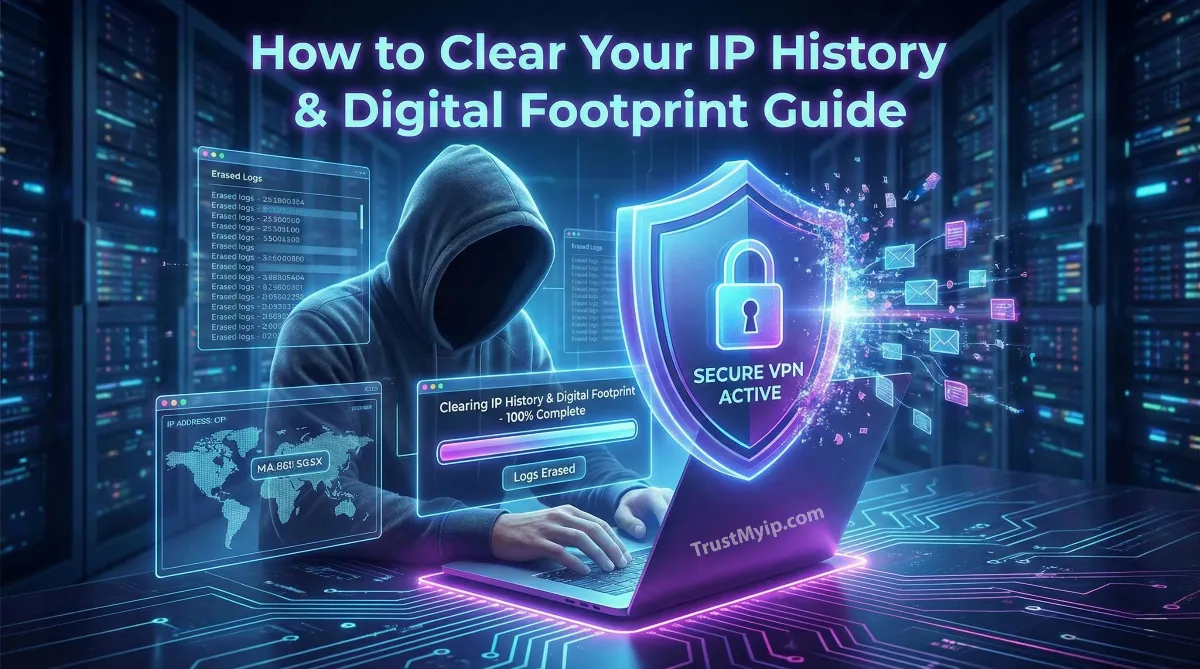
How to Clear Your IP History and Digital Footprint in 2026

Can Someone Find Your House Address Using Just Your IP? The 2026 Forensic Guide
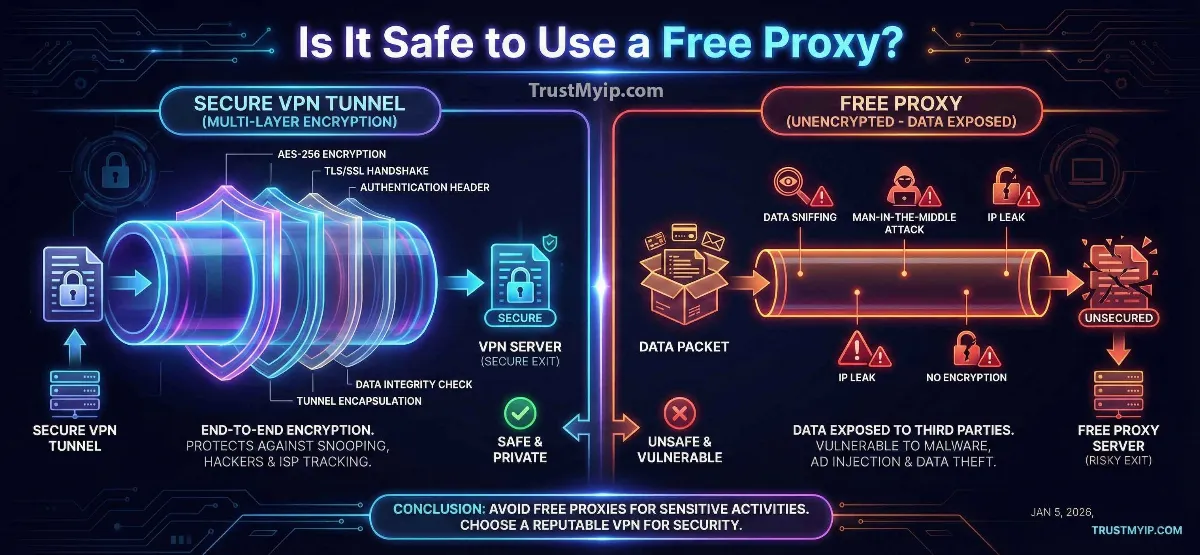
Is It Safe to Use a Free Proxy? 2026 Security Guide and Safer Alternatives

Why Is My IP Address Blocked by Websites? Complete Fix Guide 2026
