Robert Harrison
OSINT & Network Utility Expert
Professional Background
I Work at the Layer Most People Never See
My name is Robert Harrison. I am a network infrastructure specialist and OSINT researcher based in Boston, Massachusetts, with over 18 years of hands-on experience in DNS architecture, port security, network reconnaissance, and open-source intelligence methodology. Most people interact with the internet through browsers and apps. My work happens several layers below that — at the level of records, ports, protocols, and the infrastructure decisions that determine whether a network is solid or quietly broken.
I came up through systems administration and network engineering before moving into security-focused infrastructure work. That path gave me something that purely security-focused roles often miss: a deep understanding of how networks are actually built and operated day-to-day, not just how they fail under attack. At Trust My IP, I bring that operational perspective to every tool guide, diagnostic walkthrough, and OSINT methodology I publish.
Where My Work Is Focused
My core responsibility at Trust My IP is the technical infrastructure layer — the tools, protocols, and diagnostic methods that underpin everything else on the platform. Specifically:
- DNS Architecture & Troubleshooting: Deep-dive diagnostics on A, AAAA, MX, TXT, CNAME, and NS records — covering not just what each record does, but how misconfiguration at the DNS layer causes the cascading failures that are hardest to diagnose without knowing where to look.
- Port Security & Attack Surface Mapping: Systematic port scanning methodology — identifying exposed services, evaluating whether open ports represent legitimate functionality or unintended risk, and understanding what an attacker sees when they map your infrastructure before you do.
- OSINT & Network Reconnaissance: Using open-source intelligence frameworks to gather accurate, legally obtained information about domains, IP ranges, ASNs, and hosting infrastructure — the same techniques used in penetration testing and corporate due diligence.
- Network Utility Tools: Building and documenting diagnostic tools — hash generators, ping utilities, subnet calculators, WHOIS lookups — with a focus on returning data that is actually useful for diagnosis, not just data that looks complete.
- SSL/TLS Certificate Analysis: Certificate chain validation, expiry monitoring, cipher suite evaluation, and what misconfigured SSL actually exposes in practice versus what the browser warning tells you.
How I Think About Technical Writing
There is a version of technical writing that explains every concept from first principles and a version that assumes you already know everything. Neither is useful. The reader trying to diagnose a DNS propagation failure at 11pm does not need a history of the DNS protocol — but they do need to understand enough about how TTL caching works to know why their fix has not shown up yet and how long they should actually wait.
I write guides the way I would explain something to a colleague who is technically capable but working outside their specialty. Enough context to understand the mechanism, direct enough to get to the fix without unnecessary detours. When a diagnostic step requires a specific command or tool output, I show exactly what it looks like and what to look for in the result — not just what to run.
18 Years of Watching Infrastructure Decisions Age
One advantage of working in network infrastructure for as long as I have is that I have watched a lot of architectural decisions play out over time. Choices that seemed reasonable in 2010 created significant security debt by 2020. Protocols that were considered secure became liabilities. Configurations that were industry standard became attack vectors. That longitudinal perspective shapes how I evaluate current tools and methods — I am less interested in what works today and more interested in what is likely to hold up.
Outside the Terminal
When I step away from the monitors, I am usually in my workshop. I restore old mechanical watches and work on a vintage car that has been in various states of almost-finished for longer than I care to admit. There is a real overlap between that kind of work and network diagnostics — both require working systematically through a system you did not design, with incomplete documentation, until you find the one thing that is causing everything else to not work. Boston is a good city for people who like to fix things. I have never run out of things to fix.
Expertise Focus
"Robert Harrison is a network infrastructure specialist and OSINT researcher based in Boston, Massachusetts, with over 18 years of experience in DNS architecture, port security, and network reconnaissance. At Trust My IP, he leads the technical utility layer — building and documenting diagnostic tools and publishing hands-on guides for DNS troubleshooting, port scanning, SSL analysis, and open-source intelligence methodology. His work is grounded in systems administration and network engineering experience that predates most of the security frameworks in use today."
Article Impact
Latest from Robert

How to Change Your IP Address on a Chromebook: 3 Proven Methods for 2026 (Chrome OS Guide)

IPv4 Address Exhaustion: Why IPv6 Matters in 2026 — Complete Guide
What is APIPA Address? 169.254.x.x Explained 2026
What is DHCP? How IP Addresses Are Assigned 2026

What is a Broadcast Address in Networking? 2026

What is a Loopback Address? 127.0.0.1, localhost & 0.0.0.0 Fully Explained 2026
What is a Subnet Mask? Explained Simply 2026
What is an IPv6 Address? Complete Beginner Guide 2026
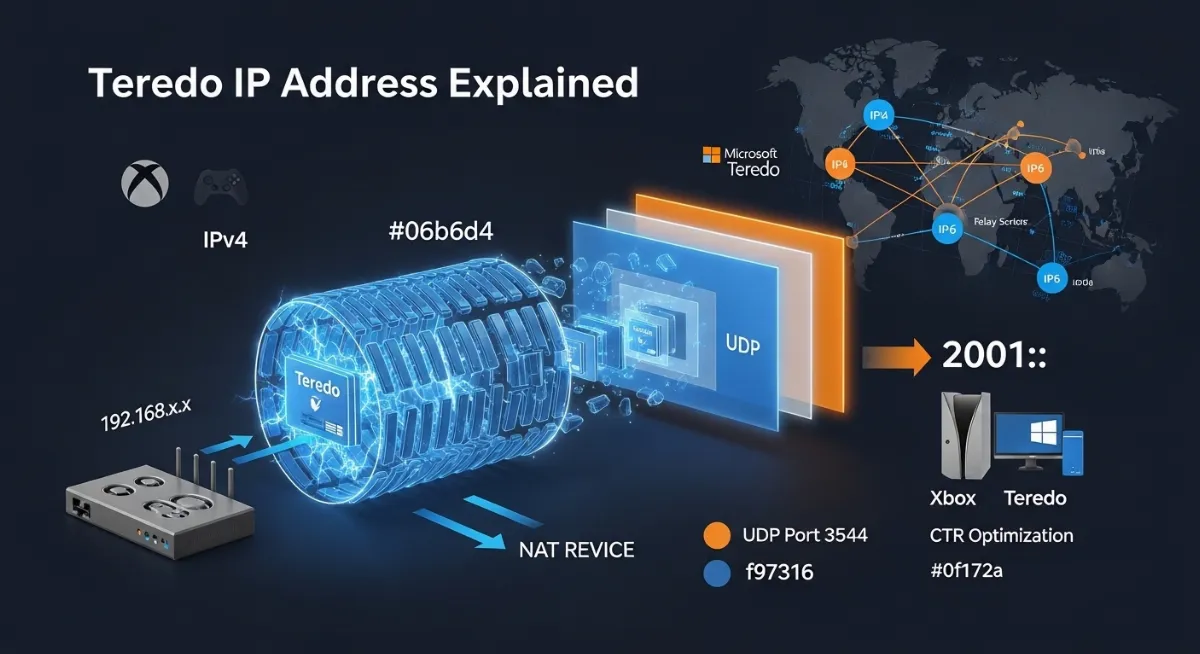
Teredo IP Address: What It Is and How to Fix Connection Errors
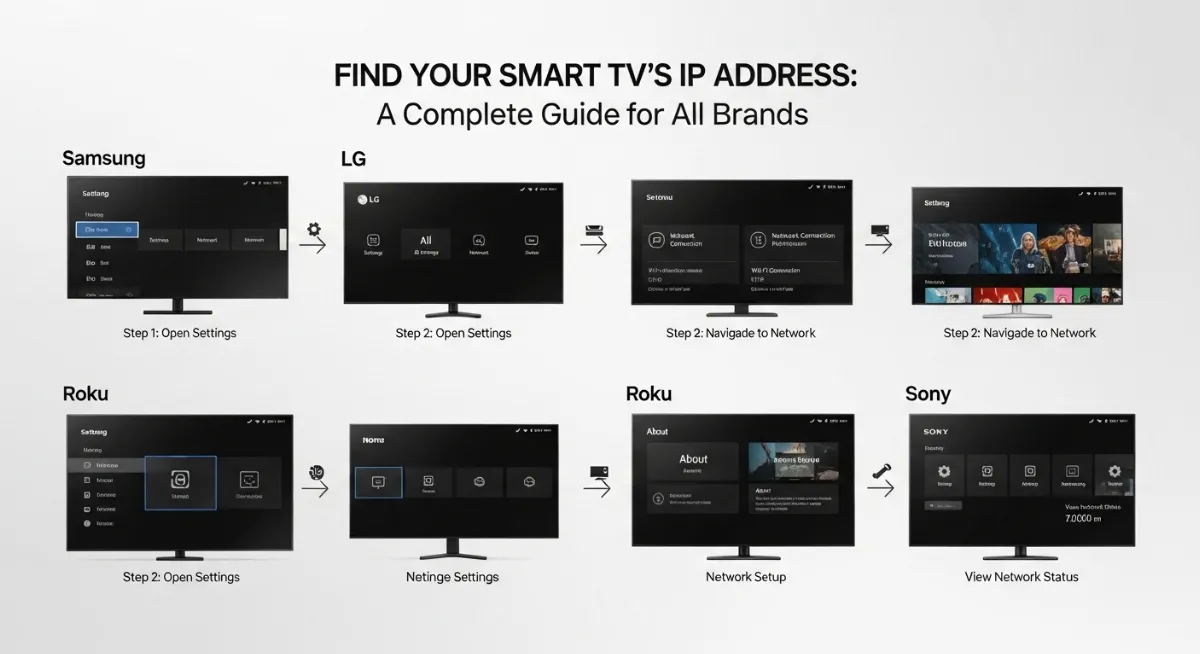
How to Find IP Address of Smart TV: Complete Guide for All Brands (2026)
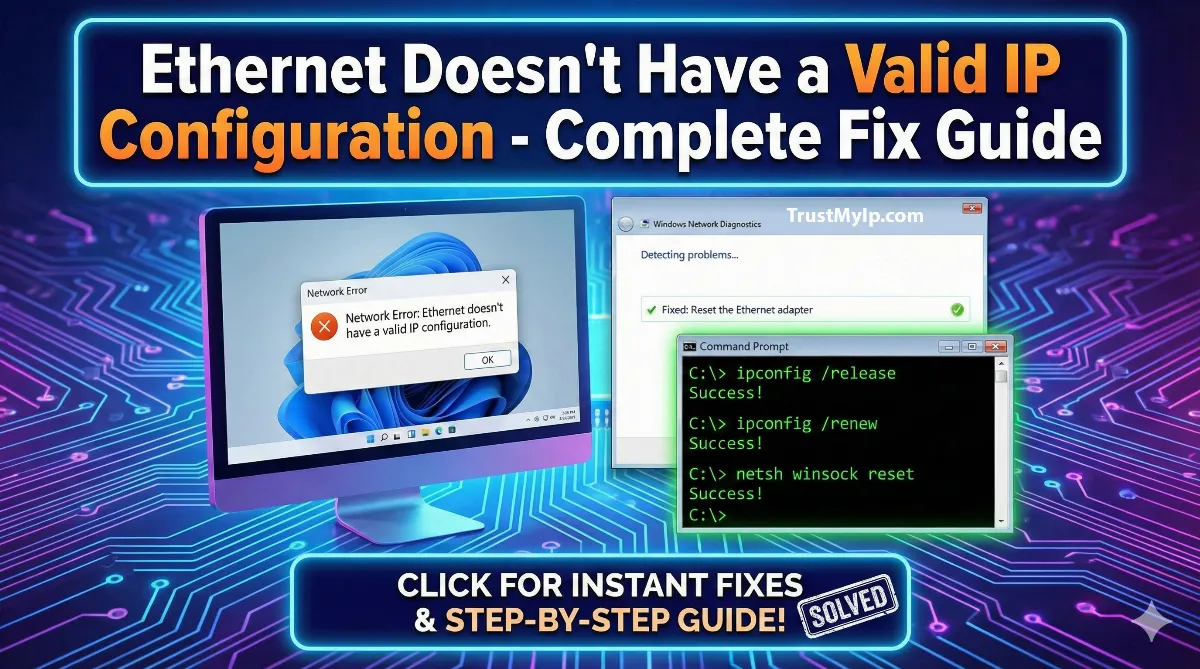
Ethernet Doesn't Have a Valid IP Configuration: 11 Fixes That Work in 2026
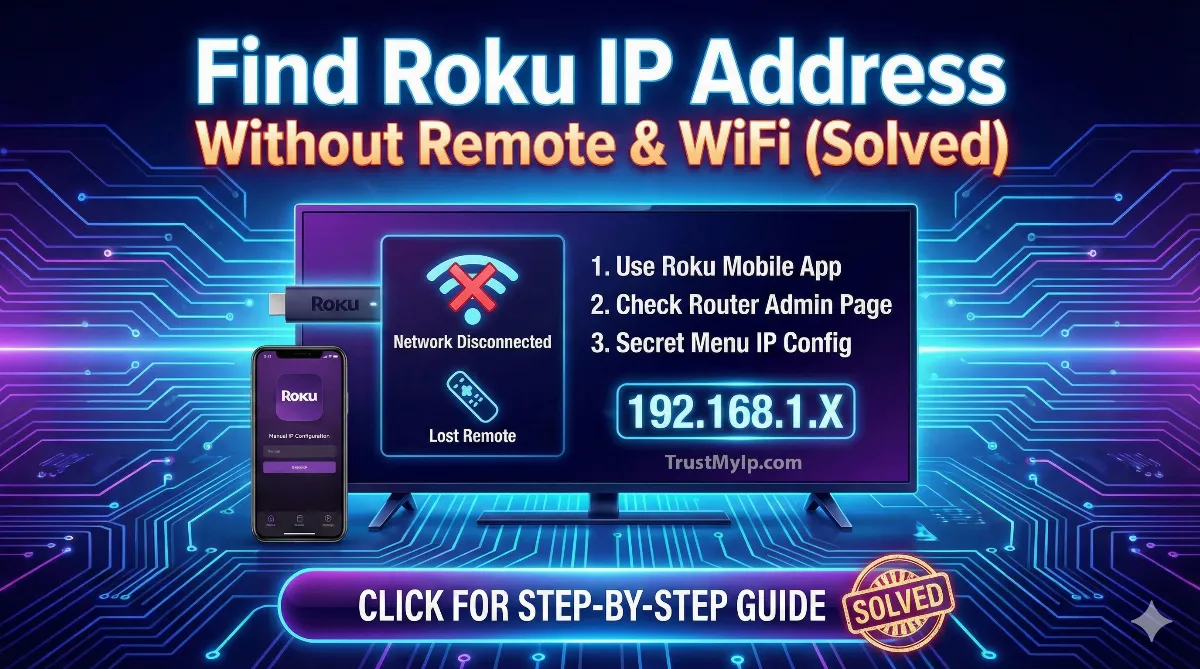
Where to Find Roku IP Address Without Remote and WiFi
What is Google's IP Address
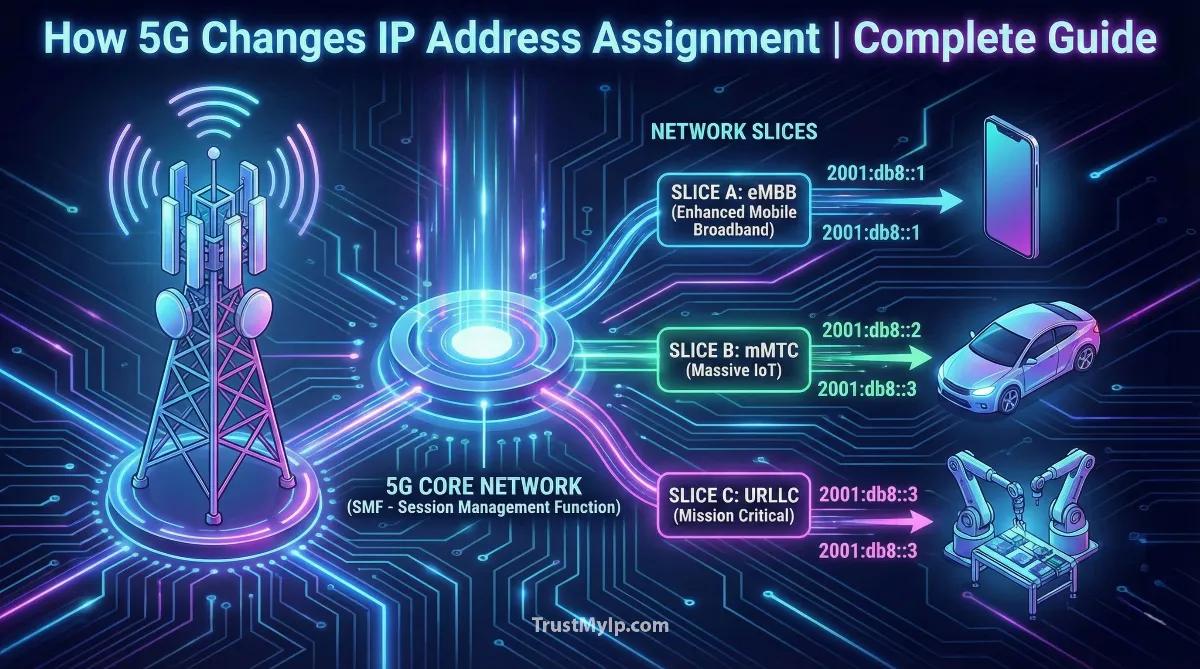
How 5G Technology Changes the Way IP Addresses are Assigned
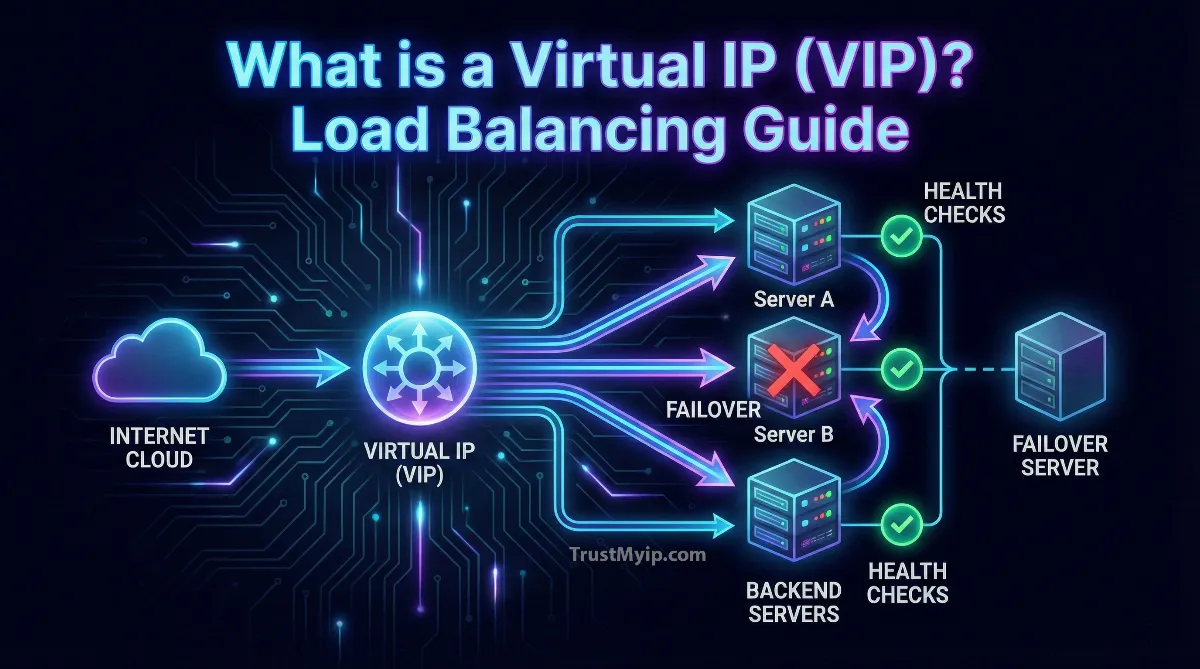
What is a Virtual IP (VIP) and How Does Load Balancing Work?
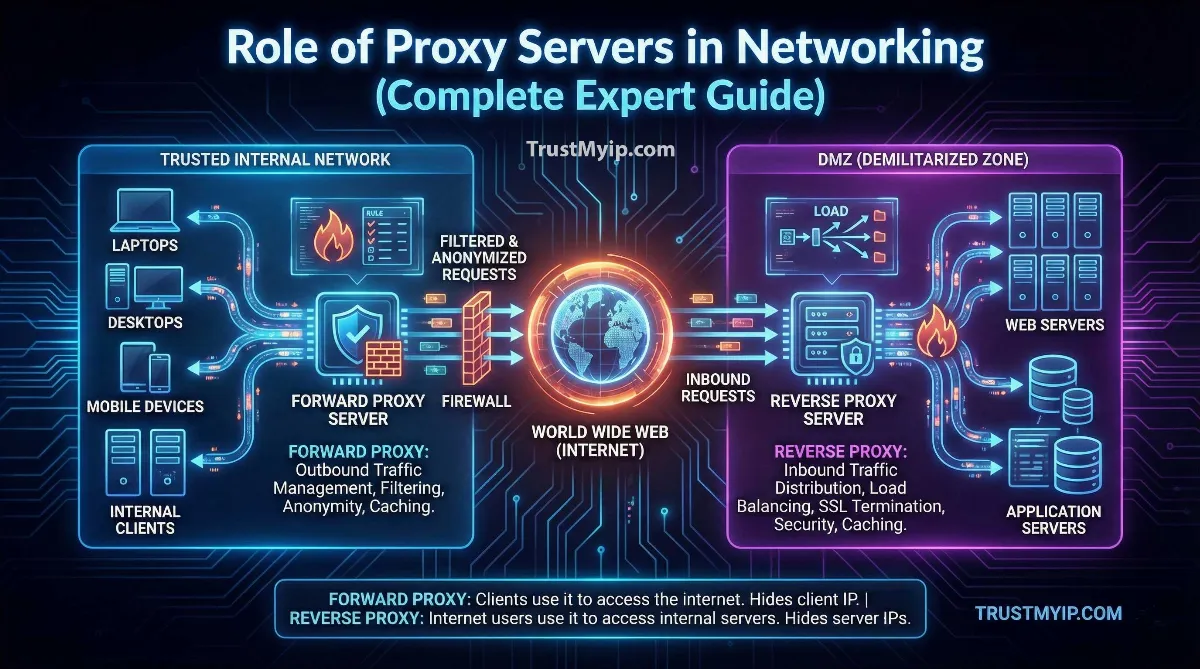
The Role of Proxy Servers in Networking: Complete 2026 Architecture Guide