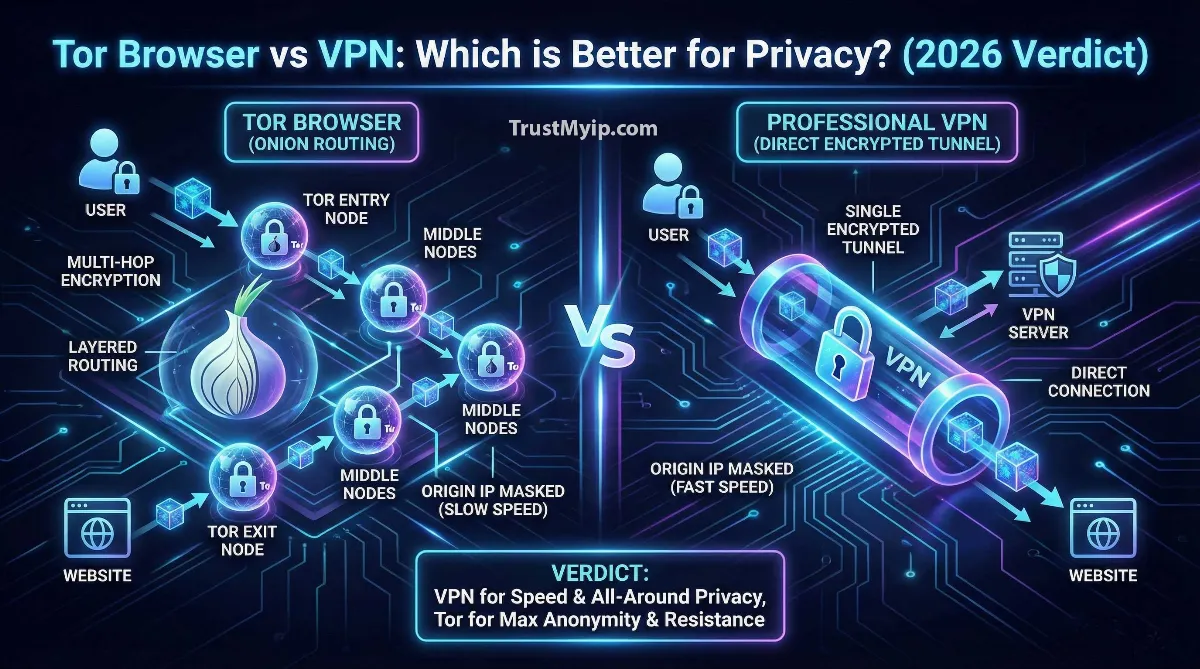
You want real online privacy — not the kind that just hides your IP from one website, but the kind that makes you genuinely untraceable. Two tools promise to deliver this: Tor Browser and a VPN. Both can hide your identity online. Both route your traffic through intermediary servers. But they do it in completely different ways — and those differences determine whether you get true anonymity or just the illusion of it.
The Tor vs VPN debate is not a matter of one being better than the other. It is a matter of understanding exactly what each tool protects, what it leaves exposed, and which threat model you are actually defending against. Getting this wrong does not just waste your time — it can leave you thinking you are protected when you are completely visible.
This guide covers everything: how Tor and VPNs work at the technical level, a direct feature comparison, the exact use cases for each, the risks of combining them, and how to check whether your current setup is actually protecting your identity right now.
Quick Answer: Tor Browser vs VPN — Which Is Better?
Use a VPN for everyday privacy — fast, encrypted browsing that hides your activity from your ISP and masks your IP from every website you visit. Use Tor Browser when you need maximum anonymity — journalists, whistleblowers, or anyone in a high-surveillance environment who needs to be completely untraceable, even from the VPN provider itself.
The key difference: a VPN requires you to trust the provider. Tor requires you to trust no one — its decentralized relay system means no single point can see both who you are and what you are doing. The tradeoff is speed: Tor is significantly slower than any VPN. Before choosing either, check what your current IP reveals about your identity right now.

"The most dangerous mistake I see from privacy-conscious users is treating Tor and VPNs as interchangeable. They are not even close to the same tool. A VPN encrypts your traffic and hides it from your ISP — but your VPN provider can still see everything. You are shifting trust from your ISP to a company. For most people, that trade is worth it, especially when using a verified no-log provider.
Tor eliminates that trust requirement entirely through mathematical distribution — no single relay can identify you. But that architectural strength comes with a real cost: Tor is too slow for streaming, video calls, or large file transfers. I have configured both systems for clients in high-risk environments — journalists, legal teams, corporate intelligence units. The answer is almost never one or the other. It is understanding which tool fits which threat, and using them accordingly. Start by verifying what your current connection actually exposes before layering additional tools on top."
1. How Tor Browser Works: Onion Routing Explained
Tor (The Onion Router) was developed by the US Naval Research Laboratory and is now maintained by the nonprofit Tor Project. It works by encrypting your traffic in multiple layers — like an onion — and routing it through a chain of three volunteer-operated relay servers before it reaches the destination.
Each relay in the chain only knows the address of the relay before it and the relay after it. No single relay knows both your real IP address and the website you are visiting. This is the core anonymity guarantee that makes Tor fundamentally different from any VPN — it does not require you to trust any single party.
The three relays are called the Guard node (entry), the Middle relay, and the Exit node. Understanding what each one knows — and does not know — is critical for understanding both Tor's strength and its most important vulnerability.
What Each Tor Relay Knows
Guard Node (Entry Relay): Knows your real IP address. Does NOT know what website you are visiting or what data you are sending. Only knows the address of the next relay in the chain.
Middle Relay: Knows only the Guard node's address and the Exit node's address. Knows nothing about your identity or destination. Acts as a pure routing buffer.
Exit Node: Knows the destination website and the data being sent. Does NOT know your real IP address — only the Middle relay's address. This is Tor's critical weakness: if the exit node operates a malicious server and you visit an HTTP (not HTTPS) site, it can read your traffic in plaintext.
The Core Guarantee: No single relay can link your identity to your activity. A global observer who controls multiple relays can attempt correlation attacks — but this requires enormous resources and is not a realistic threat for most users.
2. How a VPN Works: The Encrypted Tunnel
A VPN (Virtual Private Network) creates a single encrypted tunnel between your device and a VPN server. All your traffic — from every app on your device — travels through this tunnel encrypted. The destination website sees the VPN server's IP, not yours. Your ISP sees only encrypted data going to the VPN server — not what websites you visit.
Unlike Tor's three-relay chain, a VPN uses a single server. This makes it significantly faster than Tor — encryption overhead is the only performance cost, and modern protocols like WireGuard keep that cost minimal. The tradeoff is the trust requirement: your VPN provider can see your traffic. If the provider logs data or receives a legal order, your privacy depends entirely on their policy and jurisdiction.
Quality VPNs address this with RAM-only servers (nothing written to disk, nothing to hand over) and independent audits of their no-log claims. But the fundamental architecture means the VPN provider is a single point of trust — something Tor eliminates by design. To see exactly what information your current IP connection reveals to websites and your ISP, use our free IP address checker.
3. Tor vs VPN: Direct Feature Comparison
Here is the complete side-by-side comparison across every metric that matters for your privacy decision.
| Feature | Tor Browser | VPN |
|---|---|---|
| Anonymity Level | ✅ Extreme — no single point can identify you | ⚠️ High — depends on provider trust |
| Speed | ❌ Very slow — 3 relay hops add major latency | ✅ Fast — 10-20% overhead with WireGuard |
| ISP Visibility | ⚠️ ISP sees Tor usage (can trigger suspicion) | ✅ ISP sees only encrypted VPN traffic |
| Provider Trust Required | ✅ None — decentralized architecture | ❌ Yes — must trust VPN provider |
| Streaming Support | ❌ Unusable — too slow for video | ✅ Excellent — designed for streaming |
| Geo-Bypass Control | ❌ Random exit country — no control | ✅ Choose specific country/city |
| Access to .onion Sites | ✅ Yes — exclusive Tor hidden services | ❌ No — cannot access dark web |
| Device-Wide Protection | ❌ Browser only — other apps unprotected | ✅ All apps — system-wide encryption |
| Cost | ✅ Free — open source, nonprofit | ⚠️ $3–$12/month for quality service |
4. Which One Should You Use? Exact Use Cases
The right choice depends on your specific situation — not a general preference for privacy. These are the exact scenarios where each tool is the correct choice.
✅ Use Tor Browser When:
- → You are a journalist or whistleblower communicating sensitive sources
- → You live in a country with heavy internet censorship or surveillance
- → You need to access .onion hidden services
- → You cannot trust any single provider — including a VPN company
- → You need maximum anonymity and speed does not matter
- → You are doing legal research on sensitive topics without leaving a trail
✅ Use a VPN When:
- → You want everyday browsing privacy from your ISP
- → You use public Wi-Fi — airports, hotels, cafes
- → You need to stream geo-restricted content with full speed
- → You want all apps protected — not just browser traffic
- → You need to bypass geo-blocks in a specific country
- → You want to prevent ISP throttling on streaming or downloads
⚠️ Do NOT Use Tor Browser For:
Streaming video, video calls, large file downloads, online banking where you need consistent identity, or any task requiring reliable speed. Tor's three-relay architecture makes it too slow for any bandwidth-intensive activity. Using Tor for these tasks will frustrate you and may cause you to abandon it before it actually protects you — which is the worst outcome.
5. Browser-Integrated Privacy Tools: Opera VPN, Brave, and Firefox
Many users consider browser-built privacy features as alternatives to Tor or a standalone VPN. In 2026, it is important to understand exactly what these tools do — and what they do not do.
| Tool | What It Actually Is | Real Protection Level |
|---|---|---|
| Opera "VPN" | An HTTP proxy — not a real VPN. Routes browser traffic only, no encryption. | Very Low — proxy-level only, logs kept by Opera |
| Brave Tor Tab | Routes one browser tab through Tor network. Less fingerprint protection than full Tor Browser. | Medium — better than nothing, worse than Tor Browser |
| Firefox (Standard) | Regular browser with optional privacy extensions. No built-in IP masking. | Low — requires significant manual hardening |
| Tor Browser | Modified Firefox routed through full Tor network with fingerprint normalization. | Very High — genuine anonymity tool |
The key takeaway: Opera's "VPN" is a marketing label on a basic proxy — not a real VPN. Brave's Tor integration is useful for quick anonymous browsing but lacks the full fingerprint protection of the dedicated Tor Browser. If anonymity matters, use the actual Tor Browser, not a browser that borrows Tor's name. To check whether your browser is currently leaking your real IP despite any privacy tool you are using, read our guide on does incognito mode actually hide your IP address.
6. Using Tor and VPN Together: Tor-Over-VPN vs VPN-Over-Tor
You can combine Tor and a VPN for layered protection. The two configurations — Tor over VPN and VPN over Tor — are very different and serve different purposes.
Tor over VPN (Recommended)
Connect to your VPN first, then open Tor Browser. Your ISP sees only VPN traffic — they cannot tell you are using Tor. The VPN provider sees you connecting to Tor but cannot see your Tor activity. This is the most practical combination: it hides your Tor usage from your ISP while preserving Tor's anonymity guarantees. Most users who combine both tools use this configuration.
VPN over Tor (Advanced, Rarely Recommended)
Route your VPN connection through the Tor network. Extremely complex to configure, significantly slower, and provides very limited benefit for most users. The VPN provider still knows your Tor exit IP, and the configuration is fragile. Only relevant for very specific threat models that require hiding your VPN usage even from Tor exit nodes — a scenario that applies to almost no one outside of highly specialized security work.
7. Tor and VPN Failure Points: What Can Expose You
Both Tor and VPNs can fail — and the failures are often silent. You think you are protected while you are completely visible. These are the most common exposure points that break anonymity even when using these tools correctly.
-
DNS Leaks
Your browser can make DNS requests that bypass both Tor and your VPN — sending your real location to your ISP's DNS server even while your IP appears masked. Run our DNS lookup tool to check whether your DNS is leaking your real identity right now.
-
WebRTC IP Leaks
Browser WebRTC connections can reveal your real local and public IP even with a VPN or Tor active. This is one of the most common ways VPN protection gets bypassed silently. Use our WebRTC leak test to verify your browser is not exposing your real IP through this channel.
-
Malicious Tor Exit Nodes
Anyone can operate a Tor exit node. A malicious exit node can read all unencrypted HTTP traffic passing through it. Always verify you are visiting HTTPS sites when using Tor — never enter credentials or sensitive data on HTTP pages while on Tor.
-
Browser Fingerprinting
Your browser's unique combination of screen size, fonts, installed plugins, timezone, and language settings creates a fingerprint that identifies you even when your IP is masked. Tor Browser normalizes these signals to make every user look identical — standard browsers do not. Even with a VPN, your browser fingerprint can uniquely identify you across sessions.
-
IP Reputation Damage From Shared IPs
VPN and Tor exit IPs are heavily blacklisted across major websites. When you connect, you may inherit the poor reputation of thousands of previous users. Websites block you, serve CAPTCHAs constantly, or log your suspicious connection — defeating the purpose of using the tool at all. Read our full guide on how IP reputation scoring works and why it affects even anonymous connections.
Conclusion: Tor for Anonymity, VPN for Privacy — Know the Difference
The Tor vs VPN debate resolves cleanly once you understand what each tool actually does. Tor provides true anonymity by distributing trust across a decentralized relay network — no single party can link your identity to your activity. VPNs provide privacy by encrypting all your traffic and hiding your activity from your ISP — but they require trust in the provider.
For most people in most situations, a quality VPN is the right choice. It is fast, easy to use, protects all apps on your device, and provides genuine privacy from ISP monitoring and website tracking. For the small number of users who genuinely need to be untraceable — journalists, activists, researchers — Tor Browser is the correct tool, used with realistic expectations about speed.
Combining both — Tor over VPN — gives you ISP-level privacy plus Tor's anonymity guarantees. It is slower than VPN alone but significantly more protective than either tool used in isolation. If you choose this route, use a verified no-log VPN from our guide on the top 5 VPNs for privacy in 2026.
Whichever tool you use, check your actual protection status — not just the app icon in your taskbar. DNS leaks, WebRTC exposure, and IP reputation damage can silently bypass any privacy tool. Start with our free IP checker to see what your current connection reveals. If your IP is already on blacklists from shared VPN pools, follow the steps in our guide on improving a damaged IP reputation score before layering additional privacy tools.
True privacy in 2026 is not about picking the right tool — it is about understanding what your tool actually does, verifying it is working, and knowing its limits before you rely on it.
Is Your Setup Actually Protecting You?
Check your real IP exposure, DNS leaks, and WebRTC vulnerabilities right now. Know exactly what your Tor or VPN connection is — and is not — protecting.