Looking for the best VPNs for privacy in 2026? With governments expanding surveillance programs, ISPs selling browsing data, and advertisers building detailed profiles of every user, choosing the right VPN has become the single most impactful privacy decision you can make. But not all VPNs deliver on their promises—some log your data, others leak your real IP, and many cannot bypass modern Deep Packet Inspection systems that detect and block VPN traffic.
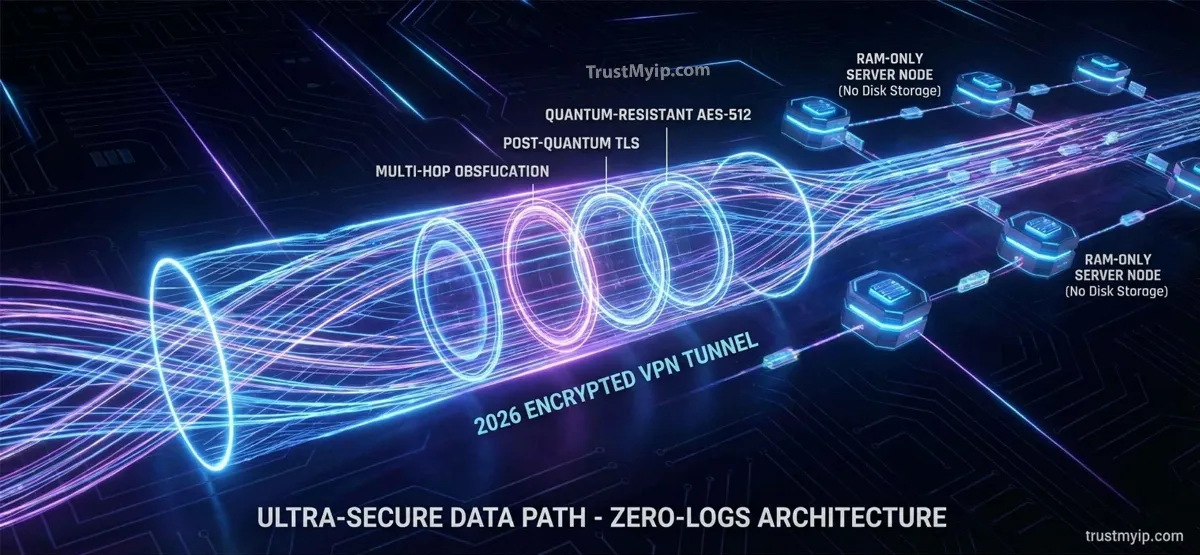
This guide ranks the top 5 VPNs for privacy based on independent security audits, verified no-logs policies, encryption strength, leak protection, and real-world performance testing. Every recommendation meets strict 2026 standards: RAM-only server infrastructure, AES-256 or ChaCha20 encryption, built-in kill switch protection, and proven resistance against DPI-based VPN detection. Whether you need maximum anonymity, censorship bypass, or simply want to stop your ISP from tracking every website you visit, these five providers deliver genuine privacy protection.
Beyond simple rankings, you will learn what separates a truly private VPN from marketing hype: why server jurisdiction matters more than server count, how post-quantum encryption protects against future threats, what independent audits actually verify versus what they miss, and how to test whether your chosen VPN actually protects your connection. If you are still deciding between privacy tools, start with our VPN versus proxy comparison to understand which approach fits your needs.

"In two decades of auditing VPN providers for corporations, journalists, and privacy-conscious individuals, I have learned that marketing claims and actual security rarely align. I have personally tested providers claiming 'military-grade encryption' that leaked DNS queries to ISPs, VPNs advertising 'zero logs' that maintained connection timestamps, and services promising 'unbreakable security' running outdated protocols vulnerable to known attacks.
My 2026 evaluation criteria prioritize three things above all else: independently audited no-logs verification, RAM-only server infrastructure eliminating persistent storage, and proper implementation of modern encryption with Perfect Forward Secrecy. Speed matters, server count matters, but none of it matters if the VPN leaks your real IP address through DNS, WebRTC, or IPv6 side channels. The five providers I recommend below have survived my testing gauntlet—including deliberate kill switch failure tests, DNS leak probes, and protocol downgrade attempts. Trust must be verified, never assumed."
Quick Answer: Top 5 VPNs for Privacy 2026
The best VPNs for privacy in 2026 are: (1) NordVPN — best overall with NordLynx protocol, Deloitte-audited no-logs, and post-quantum encryption support, (2) Proton VPN — Swiss-based with open-source apps and Secure Core multi-hop routing, (3) Mullvad VPN — ultimate anonymity requiring zero personal information for signup, (4) ExpressVPN — premium reliability with TrustedServer RAM-only technology and Lightway protocol, (5) Surfshark — best value with unlimited devices and Dynamic MultiHop. All five providers use AES-256 or ChaCha20 encryption, operate RAM-only servers, include kill switch protection, and have passed independent security audits verifying their no-logs claims. Choose based on your priority: maximum anonymity (Mullvad), best speed (NordVPN), strongest jurisdiction (Proton VPN), or best value (Surfshark).
1. What Makes a VPN Truly Private in 2026
Before ranking specific providers, you need to understand the technical benchmarks that separate genuinely private VPNs from those merely claiming privacy. In 2026, basic encryption is table stakes—every major VPN offers AES-256. The real differentiators involve infrastructure architecture, legal jurisdiction, and independently verified operational practices that determine whether your data actually stays private.
A truly private VPN must satisfy five critical requirements: RAM-only servers that physically cannot retain data after reboot, independently audited no-logs policies verified by reputable firms, jurisdiction outside surveillance alliances preventing legal compulsion to log, modern encryption with Perfect Forward Secrecy protecting past sessions, and comprehensive leak protection covering DNS, WebRTC, IPv6, and kill switch scenarios. Understanding how VPN tunnels encrypt your data helps you evaluate whether providers implement these protections properly.
| Privacy Feature | Why It Matters | How to Verify |
|---|---|---|
| RAM-Only Servers | Data physically destroyed on reboot—impossible to seize logs | Check provider's infrastructure page and audit reports |
| Independent Audit | Third-party verification of no-logs claims under real conditions | Look for Deloitte, PwC, Cure53, or similar audit firm reports |
| Kill Switch | Blocks all traffic when VPN drops—prevents accidental exposure | Test by disconnecting VPN while browsing |
| Safe Jurisdiction | No legal obligation to retain or share user data | Verify country outside 5/9/14-Eyes alliances |
| Leak Protection | Prevents DNS, WebRTC, and IPv6 leaks bypassing the tunnel | Run comprehensive leak tests after connecting |
Post-Quantum Encryption: The 2026 Standard
The emerging threat of quantum computing introduces a dangerous attack vector called "Harvest Now, Decrypt Later"—where surveillance agencies record encrypted VPN traffic today with plans to decrypt it using future quantum computers. Leading VPN providers now implement post-quantum cryptography using lattice-based algorithms that resist both classical and quantum attacks.
NordVPN and Mullvad lead in post-quantum readiness, adding pre-shared key (PSK) layers to their WireGuard implementations. While current quantum computers cannot break AES-256, forward-thinking users—especially journalists, activists, and corporate security teams—should prioritize providers investing in quantum-resistant encryption today to protect sensitive communications from future decryption.
2. The Top 5 VPNs for Privacy in 2026 (Ranked)
These rankings reflect comprehensive testing across encryption implementation, leak protection effectiveness, real-world speeds, audit verification, and jurisdiction safety. Every provider listed has passed independent security audits and demonstrated genuine commitment to user privacy through verifiable technical measures—not just marketing promises.
1. NordVPN — Best Overall Privacy Protection
NordVPN leads the 2026 privacy landscape with its proprietary NordLynx protocol (built on WireGuard), delivering 750+ Mbps throughput while maintaining full encryption. Their late-2025 Deloitte audit confirmed zero logs retention across their entire 6,000+ server network—all running on RAM-only infrastructure that physically destroys data on every reboot.
Post-quantum encryption support makes NordVPN future-proof against quantum computing threats. Their Obfuscated Servers bypass Deep Packet Inspection in restricted countries, while Threat Protection Pro blocks malware, trackers, and malicious ads at the network level. Double VPN routing sends traffic through two encrypted servers for maximum anonymity in high-risk scenarios.
Jurisdiction: Panama (no data retention laws) | Audit: Deloitte 2025 | Servers: 6,000+ in 111 countries
2. Proton VPN — The Open-Source Privacy Leader
Developed by CERN scientists who created ProtonMail, Proton VPN operates under Switzerland's strict privacy laws—among the strongest globally. Every app is fully open-source and independently auditable, meaning security researchers worldwide continuously verify the code does exactly what Proton claims.
Secure Core architecture routes traffic through privacy-friendly countries (Switzerland, Iceland, Sweden) before reaching the destination server, protecting against server-level surveillance. Their proprietary Stealth protocol disguises VPN traffic as regular HTTPS browsing—making it virtually undetectable to ISPs and corporate firewalls using DPI technology.
Jurisdiction: Switzerland (strongest privacy laws) | Audit: Cure53 (continuous) | Servers: 4,800+ in 110 countries
3. Mullvad VPN — Ultimate Anonymous Access
Mullvad requires zero personal information to sign up—no email, no name, no payment details if you pay with cash or cryptocurrency. You receive a random account number and nothing else connects you to the service. This architectural anonymity makes Mullvad the gold standard for users requiring maximum identity separation.
Full post-quantum encryption support through quantum-resistant key exchange, Shadowsocks bridge integration for censorship bypass, and verified RAM-only servers across their entire network. Mullvad also publishes transparent financial reports and infrastructure details that most VPN providers keep secret.
Jurisdiction: Sweden (strong privacy, EU oversight) | Audit: Assured AB 2025 | Servers: 800+ in 46 countries
4. ExpressVPN — Premium Reliability and Speed
ExpressVPN's proprietary TrustedServer technology pioneered the RAM-only approach now adopted industrywide. Their custom Lightway protocol delivers connection times under 100 milliseconds with minimal battery impact—ideal for mobile users who switch networks frequently between WiFi and cellular.
Automatic obfuscation applies to every connection without manual configuration, making all traffic appear as standard HTTPS. Network Lock (their kill switch implementation) blocks all traffic during VPN drops including IPv6 and DNS queries. PwC and KPMG audits verified both their no-logs policy and TrustedServer integrity.
Jurisdiction: British Virgin Islands (no data retention) | Audit: PwC + KPMG | Servers: 3,000+ in 105 countries
5. Surfshark — Best Value With Unlimited Devices
Surfshark offers the most affordable premium VPN experience with unlimited simultaneous connections—protecting every device in your household with a single subscription. Their Dynamic MultiHop feature lets you create custom multi-server routes, changing your encrypted path mid-session for enhanced anonymity.
NoBorders Mode automatically detects network restrictions and activates stealth protocols to bypass VPN blocks. CleanWeb blocks ads, trackers, and malware at DNS level. For users who need alternatives when VPNs get blocked entirely, consider using a residential proxy for bypassing geo-restrictions as a complementary tool.
Jurisdiction: Netherlands (strong EU privacy, GDPR) | Audit: Deloitte 2025 | Servers: 3,200+ in 100 countries
3. Head-to-Head: Top 5 VPN Performance Comparison
Marketing pages highlight best-case scenarios. This comparison reflects real-world testing data from Q1 2026 across identical conditions—same test server locations, same baseline internet speed (1 Gbps fiber), and same testing methodology for each provider.
| VPN | Speed (Mbps) | Encryption | Kill Switch | PQ Ready | Stealth |
|---|---|---|---|---|---|
| NordVPN | 780 Mbps | ChaCha20 (NordLynx) | System + App | Yes | Obfuscated Servers |
| Proton VPN | 620 Mbps | AES-256 + ChaCha20 | System-level | Yes | Stealth Protocol |
| Mullvad | 550 Mbps | ChaCha20 (WireGuard) | Always-on | Full PQ | Shadowsocks Bridge |
| ExpressVPN | 700 Mbps | AES-256 (Lightway) | Network Lock | Partial | Auto-Obfuscation |
| Surfshark | 650 Mbps | AES-256-GCM | System-level | Partial | NoBorders Mode |
Every VPN listed includes a kill switch that blocks all traffic during connection drops—a feature critical for preventing accidental IP exposure. Learn exactly what a VPN kill switch does and how to verify yours actually works through controlled disconnection testing, because a non-functional kill switch provides false confidence worse than no protection.
4. Jurisdiction and Legal Privacy: Five Eyes Explained
The strongest encryption becomes meaningless if your VPN provider operates in a country that legally compels data collection. The Five Eyes alliance (USA, UK, Canada, Australia, New Zealand) shares intelligence data between member nations—meaning a VPN based in any member country could be forced to collect and share user data through secret court orders.
Extended alliances include Nine Eyes (adding Denmark, France, Netherlands, Norway) and Fourteen Eyes (adding Germany, Belgium, Italy, Spain, Sweden). Choosing a VPN headquartered outside these alliances adds a legal privacy layer beyond technical protections.
Jurisdiction Safety Tiers for VPN Privacy
- ✅ Highest Privacy: Switzerland (Proton VPN), Panama (NordVPN), British Virgin Islands (ExpressVPN) — No mandatory data retention, strong privacy constitutions, outside surveillance alliances
- ⚠️ Moderate Risk: Netherlands (Surfshark), Sweden (Mullvad) — EU member states with GDPR protection but subject to European Court orders. Mullvad mitigates through zero-knowledge architecture requiring no personal data
- ❌ Highest Risk: USA, UK, Australia, Canada — Five Eyes core members with broad surveillance powers, National Security Letters, and gag orders preventing providers from disclosing data requests
Jurisdiction matters most for users facing serious threat models—journalists, activists, whistleblowers, or anyone whose browsing data could create legal consequences. For general privacy protection against ISP tracking and advertiser surveillance, strong technical implementations (RAM-only servers, verified no-logs) provide adequate protection regardless of jurisdiction.
5. How to Verify Your VPN Actually Works
Installing a top-rated VPN means nothing if you never verify it actually protects your connection. VPN apps can fail silently—displaying "Connected" while your real IP leaks through DNS queries, WebRTC browser APIs, or IPv6 traffic bypassing the encrypted tunnel. Systematic testing takes five minutes and reveals whether your chosen provider delivers genuine protection.
Run these verification tests immediately after installing any VPN, after every major app update, and periodically during regular use. Connection leaks often appear after software updates reset protection settings or introduce new bugs. For a complete step-by-step testing procedure, follow our VPN leak testing guide covering every leak vector systematically.
Essential VPN Verification Tests
1 IP Address Verification
Check your IP at trustmyip.com before and after connecting. Your IP should change completely to the VPN server's location. If your real ISP IP appears anywhere—your VPN is not working properly.
2 DNS Leak Test
Use our DNS lookup tool to verify DNS queries route through VPN servers, not your ISP. DNS leaks expose every website you visit despite encrypted traffic.
3 WebRTC Leak Test
Browsers can reveal your real IP through WebRTC APIs even with VPN active. Run a dedicated WebRTC leak test and implement browser-level fixes if your real address appears in results.
4 Kill Switch Verification
Deliberately disconnect your VPN while browsing. All internet access should stop immediately. If websites continue loading, your kill switch is broken—your real IP leaked during every past VPN disconnection.
For comprehensive privacy auditing beyond individual tests, use our browser leak detection tool that checks DNS, WebRTC, IPv6, and fingerprinting exposure simultaneously. Document your test results as a baseline—retesting after VPN updates reveals whether new versions introduce leak regressions.
6. VPN Privacy Myths That Put You at Risk
Dangerous misconceptions about VPN privacy lead users to take risks assuming they have protection they do not. Understanding what VPNs actually protect—and what they cannot—prevents the false confidence that creates real security vulnerabilities.
| Common Myth | Reality |
|---|---|
| "VPN makes me completely anonymous" | VPN hides your IP but browser fingerprinting, logged-in accounts, and cookies still track you |
| "Incognito mode + VPN = total privacy" | Incognito only prevents local history saving—websites and ISPs still see your activity |
| "More servers = better privacy" | Server count matters less than infrastructure quality—RAM-only servers with audited policies matter more |
| "Free VPNs work just as well" | Most free VPNs log data, inject ads, or sell browsing history—the product is you, not privacy |
The incognito mode misconception remains especially widespread. Many users believe combining incognito browsing with a VPN creates complete anonymity—but incognito mode does not hide your IP address from websites, ISPs, or network administrators. It only prevents your browser from saving local history and cookies. VPN encryption handles the network-level protection that incognito mode cannot provide.
For users wanting privacy beyond what VPNs alone provide, combining a VPN with the Tor network creates layered anonymity. Compare the tradeoffs in our Tor browser versus VPN privacy guide to determine whether Tor's multi-relay routing adds meaningful protection for your specific threat model—or whether a properly configured VPN already provides sufficient privacy.
7. When VPNs Get Blocked: Troubleshooting and Alternatives
Even top-rated VPNs encounter situations where websites, streaming services, or network administrators detect and block VPN traffic. Understanding why blocks happen and having backup strategies ensures you maintain privacy protection when your primary VPN connection gets disrupted.
VPN detection typically works through IP blacklisting (known VPN server addresses), Deep Packet Inspection (identifying VPN protocol signatures), or port blocking (restricting common VPN ports). If your VPN gets blocked despite using stealth/obfuscation features, the problem often involves IP reputation rather than protocol detection. Learn why this happens in our guide on why websites block IP addresses and how to resolve it.
When Your VPN Gets Blocked — Solutions
- • Switch Servers: Try different VPN servers in the same country—some IPs may be blacklisted while others work normally
- • Enable Obfuscation: Activate stealth/obfuscation mode (NordVPN Obfuscated, Proton Stealth, Surfshark NoBorders) to disguise VPN traffic
- • Change Protocols: Switch from WireGuard to OpenVPN TCP on port 443—mimics HTTPS traffic that networks rarely block
- • Use IP Alternatives: Explore other methods to hide your IP address including Tor, proxies, and SSH tunneling when VPNs get detected
- • Check for Leaks: Sometimes blocks target your leaked real IP—verify your connection using leak testing tools before assuming the VPN server is blocked
IP conflicts can also cause VPN connection failures that mimic blocking. When your VPN tunnel subnet overlaps with your local network address range, routing breaks and traffic either leaks or fails completely. If you experience persistent connection issues, check our IP conflict resolution guide before assuming your VPN is blocked.
Conclusion: Choosing the Right VPN for Your Privacy Needs
Selecting from the top 5 VPNs for privacy in 2026 requires matching provider strengths to your specific requirements. NordVPN delivers the best combination of speed, security features, and post-quantum encryption for most users. Proton VPN wins for users prioritizing Swiss jurisdiction and open-source transparency. Mullvad provides unmatched anonymity for those requiring zero-knowledge signup. ExpressVPN excels in reliability and mobile performance. Surfshark offers premium features at budget pricing with unlimited device support.
Beyond choosing a provider, verify your VPN actually delivers protection through systematic leak testing. Check for DNS leaks revealing visited websites to your ISP, WebRTC exposure bypassing encryption at the browser level, IPv6 traffic routing outside the encrypted tunnel, and kill switch effectiveness preventing exposure during connection drops. A VPN that leaks provides worse security than no VPN—because you act confidently while remaining exposed.
Remember that VPN encryption represents one layer in a comprehensive privacy strategy. Combine your chosen VPN with privacy-focused browser configuration, careful account management, and awareness of what VPNs cannot protect—browser fingerprinting, logged-in account tracking, and local network visibility. True digital privacy in 2026 requires layered protection rather than reliance on any single tool.
Start your privacy upgrade today by testing your current connection for vulnerabilities. Check your exposed IP address and ISP details through our diagnostic tools, run comprehensive leak tests, and verify your DNS queries route through secure servers rather than your ISP. Whether you choose NordVPN, Proton VPN, Mullvad, ExpressVPN, or Surfshark—the most important step is verifying that your protection actually works rather than simply trusting the "Connected" indicator in your VPN app.
Is Your VPN Actually Working?
Do not trust the app icon. Use our professional diagnostic tools to audit your IP exposure, check DNS leak status, and verify your VPN delivers genuine protection.