Every time you load a website, stream video, or send an API request, your traffic likely passes through at least one proxy server without you realizing it. The role of proxy servers in networking extends far beyond simple IP masking—these intermediary systems power content delivery networks serving billions of requests daily, enforce corporate security policies protecting sensitive data, balance traffic loads across global server farms, and cache frequently accessed content to reduce latency by orders of magnitude.
In 2026, proxy servers have become the foundational infrastructure layer of the modern internet. Cloudflare processes over 57 million HTTP requests per second through its reverse proxy network. AWS Application Load Balancers distribute traffic across millions of backend instances using proxy architecture. Akamai's proxy-based CDN delivers between 15-30% of all global web traffic. Understanding how these systems work—and when to deploy them—gives you practical knowledge applicable to everything from enterprise network design to personal privacy protection.
This guide covers proxy server architecture from OSI layer mechanics to real-world deployment patterns, explains the critical differences between forward and reverse proxies, and maps every major proxy role in modern networking. Whether you manage enterprise infrastructure or simply want to understand how your traffic moves across the internet, this comprehensive breakdown reveals how proxy servers shape every online interaction.

"After two decades building and auditing network infrastructure for government agencies and Fortune 500 enterprises, I view proxy servers as the single most versatile component in modern networking. They simultaneously solve problems across security, performance, privacy, and reliability—no other technology addresses all four domains with a single deployment.
What most people miss about proxy servers is that the internet you experience daily is almost entirely proxy-mediated.
When you visit any major website, your request passes through multiple proxy layers: your corporate forward proxy filters outbound requests, a CDN reverse proxy like Cloudflare handles the connection, an application load balancer distributes your request to a backend server, and a caching proxy may serve the response from memory without the origin server ever being contacted. Each layer adds security, performance, and resilience. Understanding this architecture transforms how you think about network design, troubleshooting, and privacy."
Quick Answer: Role of Proxy Servers in Networking
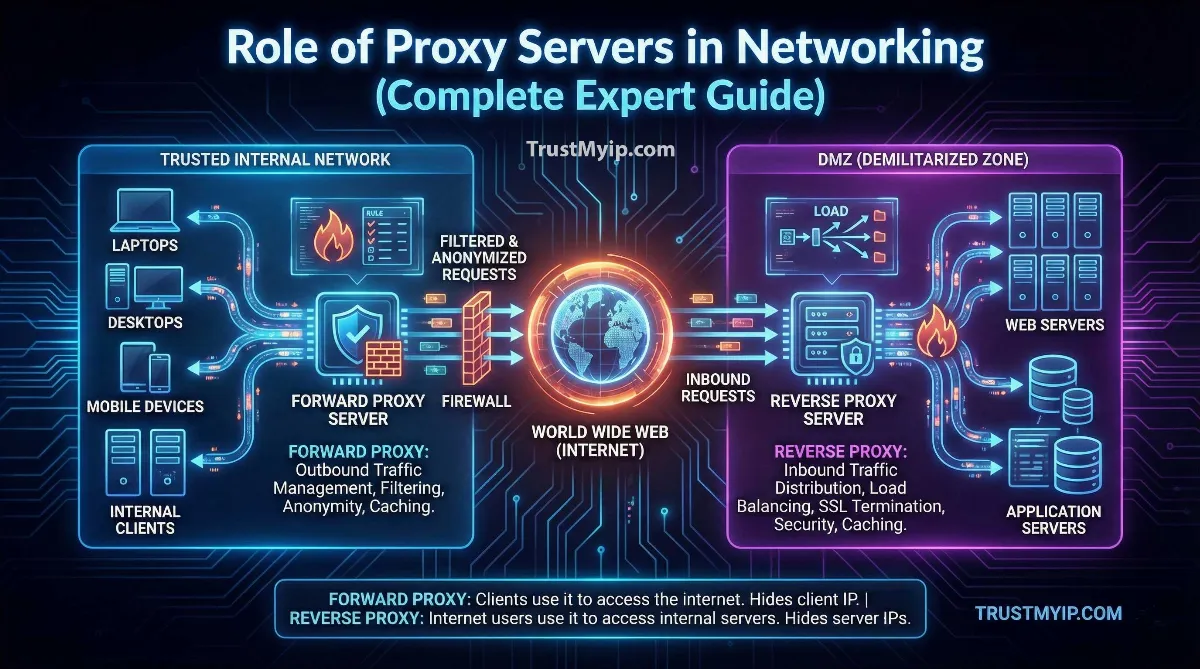
Proxy servers act as intermediaries between clients and destination servers, performing six critical networking roles: security enforcement (filtering malicious traffic and enforcing access policies), content caching (storing frequently accessed data to reduce latency), load balancing (distributing requests across multiple backend servers), SSL/TLS termination (offloading encryption processing from origin servers), anonymity and privacy (masking client IP addresses from destination servers), and traffic optimization (compressing data and managing bandwidth). Forward proxies protect clients, while reverse proxies protect servers—and modern networks deploy both simultaneously.
1. How Proxy Servers Work: OSI Layer Mechanics
A proxy server intercepts communication between a client and a destination server, processing requests through configurable rules before forwarding them. Unlike routers that simply forward packets based on IP headers, proxy servers can inspect, modify, cache, and filter traffic at multiple layers of the OSI networking model—giving them far greater control over how data moves across a network.
Layer 4 (Transport) vs Layer 7 (Application) Proxies
The layer at which a proxy operates determines what it can see and control. This distinction fundamentally shapes which networking problems each proxy type solves and how efficiently it handles traffic.
| Characteristic | Layer 4 Proxy (Transport) | Layer 7 Proxy (Application) |
|---|---|---|
| Traffic Visibility | IP addresses and port numbers only | Full HTTP headers, URLs, cookies, content |
| Routing Intelligence | Route by IP/port rules | Route by URL path, header, cookie, content type |
| Performance | Very fast (minimal processing) | Moderate (content inspection overhead) |
| Content Caching | Not possible | Full caching capability |
| SSL/TLS Handling | Pass-through only | Full termination and re-encryption |
| Example Software | HAProxy (TCP mode), iptables | Nginx, Apache, Envoy, Cloudflare |
Most production environments deploy both layers simultaneously. Layer 4 proxies handle initial connection routing with minimal latency, while Layer 7 proxies behind them perform intelligent content-based decisions. This tiered approach maximizes both speed and flexibility. Check what information your current network exposes with our IP address lookup tool.
2. Forward Proxy vs Reverse Proxy: Traffic Direction Explained
The most important classification in proxy architecture is traffic direction. Forward proxies sit in front of clients and act on their behalf. Reverse proxies sit in front of servers and protect them. Confusing these two types leads to fundamental misunderstandings about proxy deployment and capabilities.
Forward Proxy (Client-Side)
Intercepts outbound requests from users before they reach the internet. The destination server sees the proxy's IP address instead of the user's real address. Used for: employee internet filtering, bandwidth optimization, geographic content access, and personal privacy. Corporate networks deploy forward proxies to enforce acceptable use policies, monitor outbound traffic, and prevent data exfiltration.
Reverse Proxy (Server-Side)
Intercepts inbound requests from the internet before they reach backend servers. Users interact with the proxy thinking it is the actual server. Used for: load balancing, SSL termination, DDoS protection, content caching, and API gateway management. Every major website—Google, Facebook, Amazon—deploys reverse proxy arrays handling millions of concurrent connections.
Forward proxies power the privacy tools most users encounter daily. When you use a proxy service or VPN to mask your IP address, you route through a forward proxy that replaces your real IP with its own. Understanding how forward proxies enable anonymity helps you choose the right tool—compare the options in our VPN versus proxy comparison guide.
3. Six Critical Roles of Proxy Servers in Modern Networking
Proxy servers solve multiple networking challenges simultaneously. Understanding each role helps you identify which proxy deployment patterns address your specific needs—whether you manage enterprise infrastructure or need personal privacy tools.
| Role | How It Works | Proxy Type | Real-World Example |
|---|---|---|---|
| Security Enforcement | Filters malicious traffic, blocks blacklisted IPs, enforces access policies | Both | Cloudflare WAF, corporate firewalls |
| Content Caching | Stores copies of frequently requested content, serves from memory | Both | Akamai CDN, Squid proxy |
| Load Balancing | Distributes requests across backend servers using round-robin, weighted, or health-based algorithms | Reverse | Nginx, HAProxy, AWS ALB |
| SSL/TLS Termination | Decrypts HTTPS at the proxy, forwards plain HTTP to backend servers | Reverse | Let's Encrypt via Nginx, Envoy |
| Privacy & Anonymity | Replaces client IP with proxy IP, hides origin identity from destination | Forward | Residential proxies, Tor relays |
| Traffic Optimization | Compresses data, manages bandwidth allocation, prioritizes traffic types | Both | WAN accelerators, ISP proxies |
Security and Access Control
Proxy servers inspect every packet passing through them, comparing traffic against security rules, IP blacklists, and behavioral patterns. Corporate forward proxies block employees from accessing malicious websites, while reverse proxies like Cloudflare's WAF (Web Application Firewall) protect servers from SQL injection, cross-site scripting, and DDoS attacks. If your IP has been flagged by a proxy-based security system, understand the mechanisms behind blocking in our IP blocking explanation guide.
Privacy and Anonymity
Forward proxies enable privacy by replacing your real IP address with the proxy's address in all outbound requests. This fundamental capability powers every proxy-based privacy tool: residential proxies for data collection, SOCKS5 proxies for general anonymity, and web proxies for quick IP masking. The quality of anonymity depends entirely on proxy type—learn the differences in our guide explaining what residential proxies are and why you need one. For lightweight personal privacy solutions beyond proxy servers, explore our guide to hiding your IP address for free.
4. Proxy Types by Architecture: A Complete Classification
Beyond the forward/reverse distinction, proxy servers vary significantly in architecture, protocol support, and deployment model. Each type addresses specific networking requirements with different performance and security tradeoffs.
| Proxy Type | Protocol | Primary Use Case | Anonymity Level |
|---|---|---|---|
| HTTP/HTTPS Proxy | HTTP, HTTPS | Web browsing, content filtering, caching | Medium |
| SOCKS5 Proxy | Any TCP/UDP | General tunneling, gaming, P2P, streaming | High |
| Transparent Proxy | HTTP | ISP traffic management, content filtering | None (visible) |
| Residential Proxy | HTTP, SOCKS5 | Web scraping, geo-bypass, ad verification | Very High |
| Datacenter Proxy | HTTP, SOCKS5 | High-speed bulk operations, testing | Medium (detectable) |
| CGI/Web Proxy | HTTP | Quick browser-based IP masking, no setup | Low |
Residential proxies deserve special attention because they route traffic through genuine ISP-assigned home IP addresses, making automated requests indistinguishable from real user browsing. This architectural advantage drives their dominance in web scraping, competitive intelligence, and geo-restriction bypass. For dedicated scraping applications, our best free proxy for web scraping guide compares the most effective options. For geo-bypass specifically, see our best residential proxy for geo-block bypass comparison.
5. Real-World Proxy Deployments in 2026
Understanding proxy theory becomes practical when you see how organizations actually deploy these systems. These real-world patterns demonstrate proxy server roles across different scales and requirements.
CDN Architecture (Cloudflare, Akamai, Fastly)
Content Delivery Networks deploy thousands of reverse proxy servers across global edge locations. When a user requests a webpage, the nearest proxy serves cached content without contacting the origin server—reducing latency from hundreds of milliseconds to single digits. Cloudflare alone operates data centers in over 310 cities across 120+ countries, each running proxy infrastructure that handles DNS resolution, SSL termination, DDoS mitigation, and content caching simultaneously.
Enterprise Security (Corporate Forward Proxies)
Large organizations route all employee internet traffic through forward proxy servers running Zscaler, Blue Coat, or Squid. These proxies enforce acceptable use policies (blocking social media during work hours), prevent data loss (scanning outbound traffic for sensitive documents), log all web activity for compliance auditing, and block connections to known malware distribution sites. The proxy becomes the single enforcement point for the entire organization's internet security policy.
API Gateway Architecture (Kong, AWS API Gateway)
Modern microservices architectures use reverse proxy-based API gateways to manage communication between services and external clients. The proxy handles authentication, rate limiting, request transformation, and routing—allowing backend services to focus purely on business logic. A single API gateway proxy may route requests to dozens of backend services based on URL patterns, HTTP methods, and authentication tokens.
Satellite and IoT Networks
Satellite internet providers like Starlink deploy proxy servers to manage the unique challenges of high-latency orbital connections. Performance Enhancement Proxies (PEPs) pre-fetch data, compress content, and optimize TCP window sizes to compensate for the 20-40ms round-trip time inherent in low-earth orbit satellite links. IoT networks use lightweight proxy brokers (MQTT proxies) to aggregate thousands of sensor connections into manageable backend streams.
6. Proxy Security Risks and Safety Considerations
While proxy servers provide powerful networking capabilities, they also introduce security risks when misconfigured or operated by untrusted parties. The same traffic interception ability that enables caching and filtering also enables surveillance, data theft, and traffic manipulation by malicious proxy operators.
Proxy Security Risk Assessment
- • Traffic Interception: Any proxy server can read unencrypted HTTP traffic passing through it. Malicious proxies exploit this to harvest credentials, inject advertisements, or modify content. Always verify proxy trustworthiness—our guide on free proxy safety explains the specific risks of untrusted proxy services.
- • DNS Leak Exposure: Misconfigured proxy setups may route DNS queries outside the proxy tunnel, revealing your browsing destinations to your ISP despite IP masking. Test DNS routing through our DNS leak auditor to verify complete traffic isolation.
- • SSL/TLS Inspection Risks: Corporate proxies performing SSL inspection decrypt and re-encrypt HTTPS traffic, creating a potential surveillance point. Employees should understand that HTTPS traffic through corporate proxies is visible to network administrators.
- • IP Leak Vectors: Proxies only route traffic configured to pass through them. WebRTC connections, DNS queries, and non-proxy-aware applications may bypass the proxy entirely, exposing your real IP address to destination servers. Verify all leak vectors with our comprehensive IP leak testing guide.
- • Identity Correlation: Even when a proxy masks your IP, other identifiers like browser fingerprints, cookies, and hardware-level addresses can still identify you. Understanding the difference between MAC addresses and IP addresses clarifies which identifiers proxies can and cannot mask.
7. Troubleshooting Common Proxy Networking Problems
Proxy deployments introduce specific failure modes that differ from standard networking issues. Recognizing these patterns accelerates troubleshooting and prevents cascading problems across your network infrastructure.
- 502 Bad Gateway: The reverse proxy cannot reach the backend server. Check backend server health, verify the proxy's upstream configuration points to the correct IP and port, and confirm no firewall rules block proxy-to-backend communication.
- 504 Gateway Timeout: The backend server takes too long to respond. Increase proxy timeout values, optimize backend performance, or implement request queuing. Common in high-traffic scenarios where backend servers become overloaded.
- IP Address Conflicts: When proxy servers share subnet space with other network devices, IP conflicts disrupt routing and cause intermittent connectivity failures. Follow our IP conflict resolution guide for systematic diagnostic steps.
- SSL Certificate Errors: Reverse proxies handling SSL termination need valid certificates matching the domain. Expired or mismatched certificates cause browser warnings. Automate certificate renewal using Let's Encrypt with your proxy software.
- Proxy Authentication Failures: Forward proxies requiring credentials may reject connections when clients use incorrect or expired authentication tokens. Verify credential configuration in your browser, operating system, or application proxy settings. Test proxy connectivity with our proxy detection tool.
Conclusion: Why Proxy Servers Remain Networking's Most Versatile Tool
The role of proxy servers in networking spans every critical infrastructure function: security enforcement, performance optimization, load distribution, encryption management, privacy protection, and traffic control. No other single technology addresses this breadth of networking challenges with the flexibility that proxy architecture provides.
In 2026, proxy servers have evolved from simple request forwarders into intelligent traffic management platforms powered by machine learning, deployed at global scale through CDN networks, and integrated into every major cloud platform's infrastructure. Whether you deploy Nginx as a reverse proxy for your web application, use Cloudflare's proxy network for DDoS protection, or connect through a residential proxy for private browsing, you interact with proxy technology that has become inseparable from the internet itself.
Start by understanding your own network exposure. Check what information your current connection reveals, test for proxy and DNS leak vectors, and verify that any proxy services you use actually deliver the anonymity or performance they promise. The gap between how you think your network works and how it actually works often comes down to proxy configuration details that diagnostic tools reveal instantly.
Is Your Network Fully Protected?
Audit your proxy configuration, check for DNS leaks, and verify your IP exposure with our professional diagnostic toolkit.