Every month, millions of users search for free proxies to bypass geo-blocks, access restricted content, or add a layer of privacy to their browsing. The appeal makes sense—why pay for something when free alternatives exist everywhere? But asking is it safe to use a free proxy reveals an uncomfortable truth that most proxy list websites conveniently ignore: the majority of free proxy servers actively compromise your security rather than protect it.
A 2024 peer-reviewed study analyzing 443 free proxy services found that 79% modified user traffic in some way—injecting advertisements, tracking scripts, or stripping HTTPS encryption entirely. By 2026, the free proxy landscape has only grown more dangerous as cybercriminals recognize these services as efficient attack vectors for credential harvesting, session hijacking, and man-in-the-middle surveillance at scale.
This guide examines exactly what happens to your data when you connect through a free proxy, identifies which free proxy types carry the highest risk, and provides safer alternatives that protect your privacy without draining your wallet. If you still need proxy access for specific tasks, we explain how to evaluate free options using verifiable security criteria rather than blind trust.

"After investigating hundreds of free proxy services for security research over the past eight years, I can state this with absolute certainty: the free proxy ecosystem is one of the most effective social engineering operations on the internet today. Users voluntarily route their most sensitive traffic—banking sessions, email credentials, social media logins—through servers operated by unknown entities with zero accountability.
The operators know exactly what they are doing. They position free proxies as privacy tools while running the exact opposite: mass surveillance infrastructure disguised as helpful services. I have personally documented free proxy operators harvesting login credentials in real-time, injecting cryptocurrency mining scripts into browsed pages, and selling browsing histories to data brokers. The most sophisticated operations use SSL stripping to downgrade HTTPS connections, capturing everything from banking passwords to private messages—all while the user believes their connection is secure. The safest approach treats every free proxy as compromised until proven otherwise through independent technical verification."
Quick Answer: Is It Safe to Use a Free Proxy?
No—most free proxies are not safe. Research shows 79% of free proxy services modify user traffic through ad injection, HTTPS stripping, or data harvesting. Safe alternatives exist: reputable provider free tiers (WebShare, Bright Data trials), Tor Browser for anonymity, and browser-integrated proxies from Opera or Brave. If you must use a free proxy, verify it maintains HTTPS encryption, check for DNS leaks, test for WebRTC exposure, and never transmit login credentials or financial data through any unverified proxy connection.
1. What Happens to Your Data Inside a Free Proxy
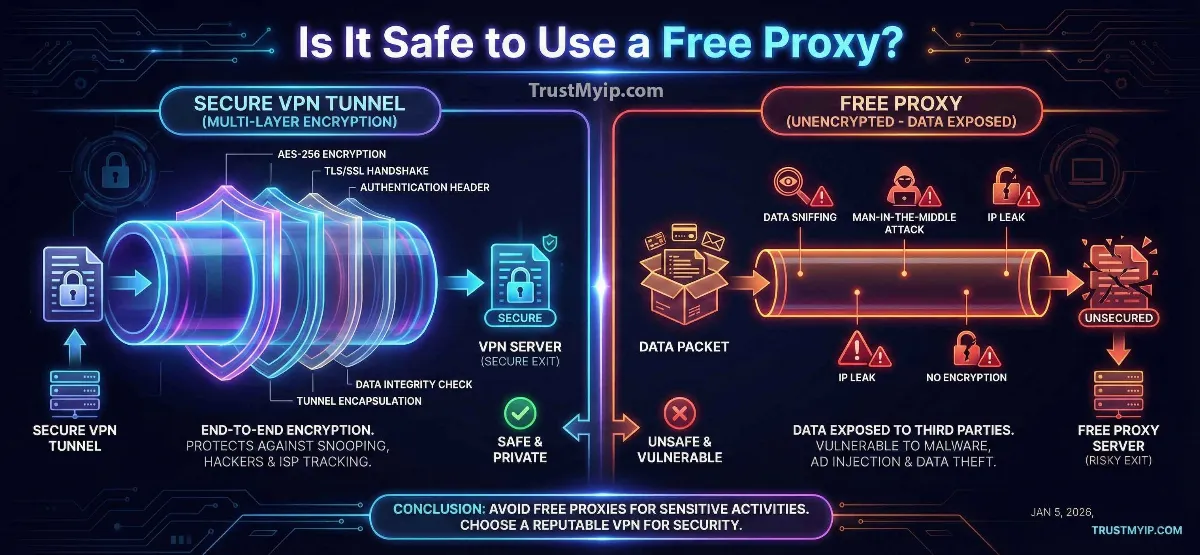
When you connect through any proxy server, every byte of your internet traffic passes through that server before reaching its destination. A trustworthy proxy simply forwards your data without inspection or modification. A malicious free proxy exploits this privileged position to intercept, analyze, modify, or record everything you send and receive.
Understanding the technical mechanisms behind free proxy abuse helps you recognize warning signs before your data gets compromised. These attack methods operate silently—your browser shows no error messages, pages load normally, and nothing visually indicates your traffic is being intercepted.
| Attack Method | How It Works | What Gets Stolen | Detection Difficulty |
|---|---|---|---|
| SSL Stripping | Downgrades HTTPS to HTTP, removing encryption between you and the proxy | Passwords, banking data, emails | Moderate |
| Session Hijacking | Copies authentication cookies to take over your logged-in accounts | Social media, email, bank accounts | Very Hard |
| Traffic Logging | Records every URL, search query, and form submission passing through | Browsing history, search patterns | Impossible to detect |
| Content Injection | Inserts ads, crypto miners, or tracking scripts into web pages | CPU resources, browsing behavior | Easy (page inspection) |
| DNS Hijacking | Redirects your DNS queries to malicious servers, sending you to fake websites | Login credentials via phishing | Moderate |
The most dangerous aspect of free proxy abuse is that multiple attack methods often operate simultaneously. A single malicious proxy might strip SSL encryption, log all traffic, inject advertisements, and hijack DNS—all while the user experiences what appears to be normal browsing. Verify your current connection integrity with our proxy leak detection tool to check whether your proxy exposes identifying information.
2. Free Proxy Types Ranked by Safety Risk
Not all free proxies carry equal risk. The source, operator, and business model behind a free proxy determine whether it genuinely serves your privacy or exploits your trust. This ranking reflects documented security incidents and structural incentive analysis—who benefits and how.
Extreme Risk: Public Proxy Lists
Free proxy lists shared on forums, Reddit threads, and proxy aggregator websites represent the highest security risk. These IPs typically belong to compromised servers, intentional honeypots operated by cybercriminals, or abandoned infrastructure with no active security maintenance. Research from 2024 confirmed that over 60% of public proxy list entries were operated by malicious actors specifically targeting users seeking anonymity.
Risk Level: Extreme | Encryption: None/Stripped | Recommendation: Never use for any purpose
High Risk: Free VPN-Proxy Apps
Mobile app stores contain hundreds of free VPN and proxy applications that monetize through aggressive data collection. These apps request unnecessary permissions (contacts, SMS, storage), sell browsing data to advertising networks, and frequently contain embedded malware. Google and Apple remove thousands of these apps annually, but new ones replace them within days.
Risk Level: High | Encryption: Varies (often weak) | Recommendation: Avoid unless independently audited
Moderate Risk: Browser-Integrated Proxies
Browsers like Opera and Brave include built-in proxy functionality backed by the company's reputation and privacy policies. These are structurally safer because the operator has a legitimate business model (browser market share) and faces accountability if caught compromising user data. However, they typically offer limited geographic options, do not encrypt all traffic, and may still collect anonymized usage data.
Risk Level: Moderate | Encryption: HTTPS maintained | Recommendation: Acceptable for casual browsing
Lower Risk: Reputable Provider Free Tiers
Established proxy providers like WebShare (10 free permanent proxies) and trial programs from Bright Data and Smartproxy offer genuinely functional free access as conversion funnels for paid plans. These companies operate under real business registrations, published privacy policies, and reputation accountability. Their free tiers use the same infrastructure as paid plans—ensuring consistent security standards. For detailed provider comparisons, see our best free proxy for web scraping guide.
Risk Level: Low | Encryption: Full HTTPS/SOCKS5 | Recommendation: Best free option available
Lowest Risk: Tor Network
The Tor Browser routes traffic through three volunteer-operated encrypted relays, making surveillance extremely difficult. No single node sees both your identity and your destination. While slower than commercial proxies, Tor provides the strongest anonymity available for free—designed specifically to resist government-level surveillance. Compare Tor's privacy architecture against VPN alternatives in our Tor versus VPN privacy comparison.
Risk Level: Very Low | Encryption: Triple-layer encryption | Recommendation: Best for maximum anonymity
3. How to Test Whether a Free Proxy Is Safe
If you decide to use a free proxy despite the risks, performing these verification checks before transmitting any sensitive data reduces your exposure significantly. Treat every free proxy as compromised until these tests confirm otherwise.
Free Proxy Safety Verification Checklist
Step 1: Verify IP Masking
Connect through the proxy, then check whether your real IP address appears anywhere in the connection metadata. Use our IP address lookup tool to confirm the proxy IP displays instead of your actual address. If your real IP appears in any header field, the proxy provides zero protection.
Step 2: Test for DNS Leaks
DNS leaks reveal your real ISP and geographic location even when your IP appears masked. Run our DNS leak detection test while connected through the proxy. If DNS queries resolve through your local ISP instead of the proxy's DNS servers, your browsing destinations remain visible to your ISP.
Step 3: Check for WebRTC Exposure
WebRTC browser APIs can leak your real IP address through peer-to-peer connections that bypass proxy routing completely. This is one of the most common leak vectors that free proxy users overlook. Run a WebRTC leak test and disable WebRTC in your browser settings before using any proxy.
Step 4: Verify HTTPS Preservation
Visit any HTTPS website through the proxy and check the padlock icon in your browser address bar. If the connection downgrades to HTTP (no padlock), the proxy performs SSL stripping—immediately disconnect and never use that proxy again. Legitimate proxies never interfere with HTTPS encryption.
Step 5: Inspect for Content Injection
Open a clean, simple webpage through the proxy and view its source code. Compare against the same page loaded directly. If additional scripts, iframes, or HTML elements appear in the proxy version, the operator injects content into your browsing—a clear sign of malicious intent.
For a comprehensive single-test approach covering multiple leak vectors simultaneously, run our complete IP leak testing guide while connected through any proxy you evaluate. This methodology catches DNS leaks, WebRTC exposure, IPv6 leaks, and proxy header leaks in one verification session.
4. Free Proxy vs VPN vs Residential Proxy: Safety Comparison
Understanding how free proxies compare against paid alternatives on concrete security metrics helps you make informed decisions based on actual protection levels rather than marketing claims. Each tool serves different privacy needs at different risk levels.
| Security Feature | Public Free Proxy | Free Tier (WebShare) | Tor Browser | Premium VPN | Residential Proxy |
|---|---|---|---|---|---|
| Encryption | None | HTTPS pass-through | Triple-layer | AES-256 | HTTPS supported |
| Traffic Logging | Almost certain | No-log policy | Technically impossible | Audited no-logs | Provider-dependent |
| IP Masking | Unreliable | Reliable | Excellent | Excellent | Excellent |
| DNS Protection | None (may hijack) | Partial | Full | Full | Provider-dependent |
| Monthly Cost | Free | Free | Free | $5-15/month | $75-800/month |
The comparison reveals a clear safety hierarchy: Tor and premium VPNs provide the strongest protection, followed by reputable free tiers, with public free proxies offering essentially zero security guarantees. For a deeper analysis of when proxies outperform VPNs and vice versa, read our VPN versus proxy comparison guide.
5. Safer Alternatives to Free Proxies in 2026
If your goal is privacy, geo-bypass, or anonymous browsing, several alternatives deliver better security than free proxies—some at zero cost. Matching the right tool to your specific need prevents both security risks and unnecessary spending.
Recommended Alternatives by Use Case
- • For General Privacy: Use a reputable VPN with independently audited no-log policies. Services like NordVPN, ProtonVPN, and Mullvad encrypt all device traffic with AES-256—far exceeding any free proxy's protection. See our top 5 VPNs for privacy 2026 rankings for tested recommendations.
- • For Maximum Anonymity: Tor Browser provides triple-layer encryption through decentralized volunteer nodes. No registration required, completely free, and designed to resist surveillance at the network level—the strongest free privacy tool available.
- • For Bypassing Geo-Blocks: Residential proxy trials from Bright Data or Smartproxy provide genuine ISP-assigned IPs that streaming platforms cannot detect. For detailed provider comparisons, read our best residential proxy for geo-block bypass guide.
- • For Web Scraping: WebShare's permanent free tier provides 10 dedicated datacenter proxies with HTTPS support and API access—structurally safer than any public proxy list for data collection tasks.
- • For Quick IP Masking: Multiple legitimate methods exist for hiding your IP without risky free proxies. Explore our complete guide to hiding your IP address for free covering VPNs, Tor, SSH tunnels, and public WiFi approaches.
6. What Free Proxies Can and Cannot Protect
Even when using a verified safe free proxy, understanding its protection boundaries prevents false confidence. Proxies—free or paid—address specific privacy threats while leaving others completely unprotected.
| Privacy Threat | Free Proxy Protection | Reality Check |
|---|---|---|
| IP Address Masking | Yes (if working correctly) | Only masks IP—other identifiers remain exposed |
| Browser Fingerprinting | No protection | Websites identify you via screen size, fonts, plugins |
| ISP Surveillance | No protection | ISP sees proxy connection (content hidden if HTTPS) |
| Geo-Block Bypass | Partial | Works on basic sites, fails against Netflix/streaming |
| Application-Level Tracking | No protection | Cookies, local storage, login sessions still track you |
The critical takeaway: even a perfectly safe free proxy only masks your IP address. It does not encrypt your traffic (unlike VPNs), does not prevent browser fingerprinting, does not block application-level tracking through cookies, and does not protect non-browser applications on your device. Understanding what a residential proxy actually does at the network level helps set realistic expectations for any proxy service.
7. Troubleshooting Free Proxy Security Issues
If you experience security-related problems while using a free proxy, these diagnostic steps help identify whether the proxy itself causes the issue or whether other configuration problems compromise your connection.
- HTTPS Websites Show as HTTP: The proxy performs SSL stripping—a man-in-the-middle attack capturing your encrypted data. Disconnect immediately, clear all cookies and saved passwords, and change credentials for any accounts accessed through that proxy. Never use that proxy again.
- Websites Show Your Real IP Despite Proxy: The proxy leaks your IP through HTTP headers (X-Forwarded-For, Via) or WebRTC connections. Check all leak vectors with our comprehensive leak testing tools. Some proxies only mask your IP in certain request types while exposing it in others.
- Unexpected Ads or Pop-ups Appearing: The proxy injects advertising content into web pages for revenue. While less dangerous than credential theft, this confirms the operator modifies your traffic—meaning they could inject malicious scripts just as easily. Switch to a verified proxy immediately.
- Websites Block You Immediately: The proxy IP has poor reputation from abuse by other users, or it belongs to a known proxy ASN range. Free proxy IPs get blacklisted rapidly because thousands of users share them simultaneously. See our IP blocking explanation guide for details.
- Network Connectivity Issues After Proxy Use: A poorly configured or malicious proxy may have modified your DNS settings or created IP routing conflicts on your local network. Follow our IP conflict resolution guide to restore normal connectivity.
Conclusion: The Honest Answer About Free Proxy Safety
Is it safe to use a free proxy? The honest answer: most free proxies are actively unsafe, and the few safe options come with significant limitations. Public proxy lists and free VPN apps represent genuine security threats that can compromise your credentials, browsing history, and financial data. The 79% traffic modification rate documented in research confirms this is not theoretical risk—it is the default behavior of free proxy services.
Safe free options do exist, but only from specific sources: reputable provider free tiers (WebShare), established privacy tools (Tor Browser), and browser-integrated proxies (Opera, Brave). Even these safer alternatives only mask your IP address without providing the comprehensive encryption, DNS protection, and traffic isolation that paid VPNs and residential proxies deliver.
Before using any free proxy, run the complete verification checklist: test IP masking, check for DNS leaks, verify WebRTC protection, confirm HTTPS preservation, and inspect for content injection. If a free proxy fails any single test, it compromises your security more than browsing without a proxy at all. For sensitive tasks involving login credentials, financial data, or private communications, invest in a trusted VPN or residential proxy—the cost of a monthly subscription is insignificant compared to the cost of compromised accounts.
Is Your Free Proxy Leaking?
Verify your proxy actually protects your identity. Test for DNS leaks, WebRTC exposure, and proxy header leaks with our professional diagnostic tools.